Installation and configuration
Datalore is available as a privately hosted service for companies on the On-Premises plan.
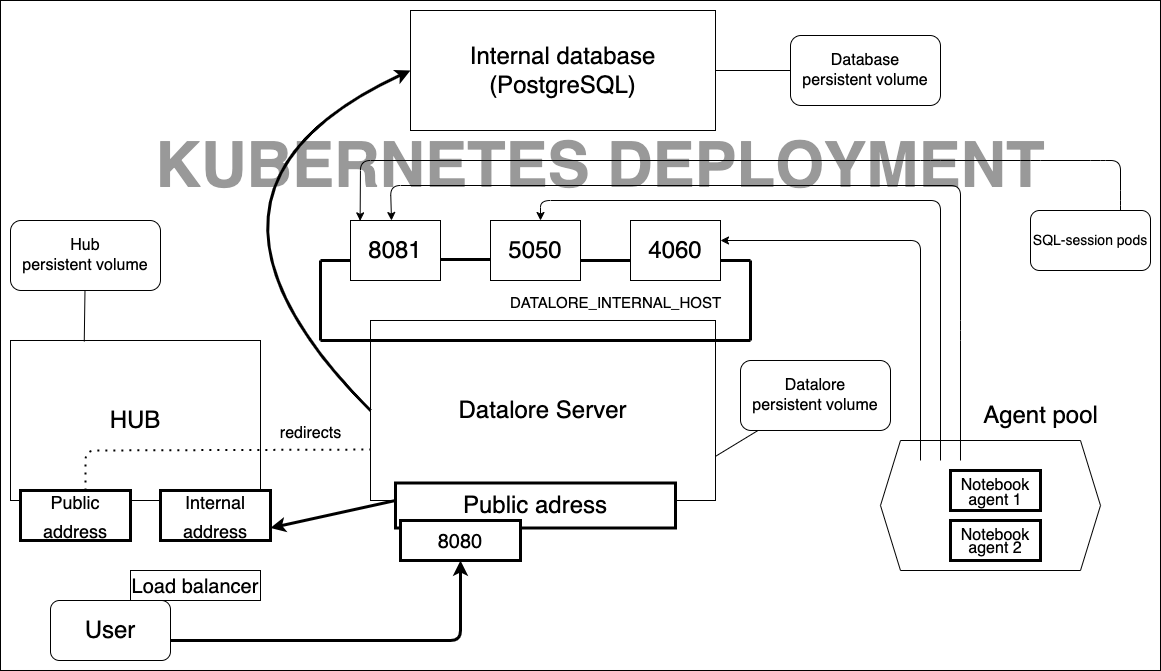
Kubernetes setup
Install Datalore on the Kubernetes cluster of your choice, be it on-premises or a private cloud. Kubernetes setup is the most customizable method, but it requires knowledge of Kubernetes technology. Find more information in our installation guide.
Here is how the Kubernetes setup looks:
Docker setup
With Docker-based installation you can get a basic, private Datalore setup running in less than 10 minutes. Whether it’s on AWS, GCP, Azure or an on-premises machine, you’ll be able to set up Datalore by running a single Docker command. Connecting authentication modules, setting up internal usage plans, and customizing environments can be further carried out step-by-step.
Availability in networks with no internet access
Datalore is available for hosting in networks that have no access to the internet.
Custom single sign-on
Configure almost any possible method of user authentication to let your team seamlessly access Datalore. The On-Premises version includes JetBrains Hub – the module for connecting authentication providers.
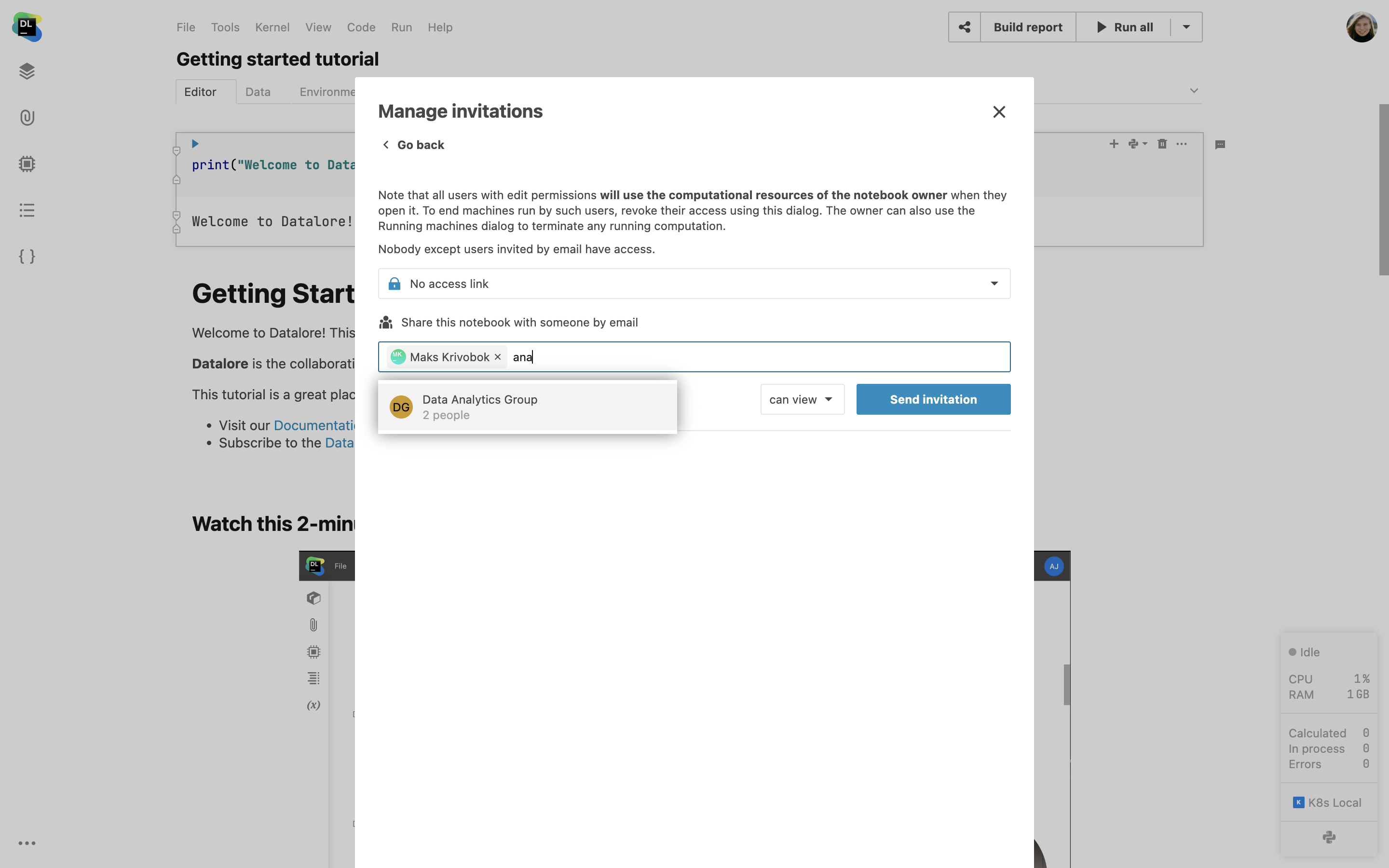
User groups support
Easily manage who can access notebooks and workspaces via group sharing. Create user groups inside Datalore’s Admin panel or sync them with the JetBrains Hub authentication module. JetBrains Hub can sync user groups for selected authentication modules with your authentication provider (e.g. Azure AD). Find more information on supported Auth modules here.
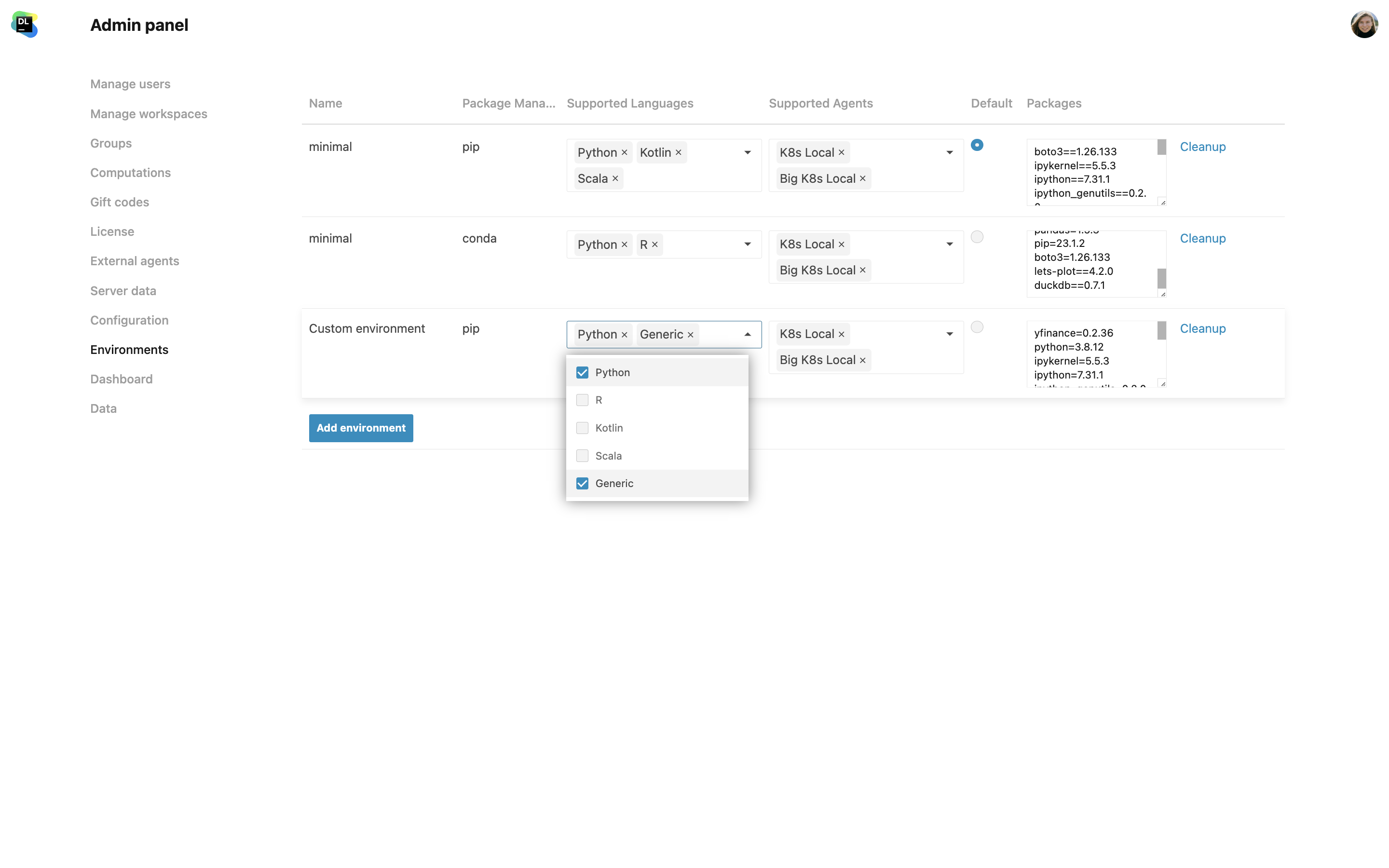
Custom environments
Create multiple base environments out of custom Docker images. You can pre-configure all the dependencies, package versions, and build tool configurations so that your team doesn’t spend time on installing things manually and syncing package versions.
Custom PyPI server configuration support
You can now set up custom PyPI server configurations in Datalore. This allows you to explore custom repositories via Datalore’s environment manager, extending beyond the default pypi.org server, directly facilitating package installation for users. Find more details in our documentation.
Internal usage plans
Different members of your data science team might need different computational resources. Datalore allows you to create separate usage plans for those who require high-efficiency GPUs and for those who need a lot of regular CPU computations, for example. You can specify how many hours each user is allowed to run each machine type, and restrict some users from running high-cost machines.

User actions log
You can turn on user action logging inside your on-premises setups. The logs will help you investigate any compliance requests.
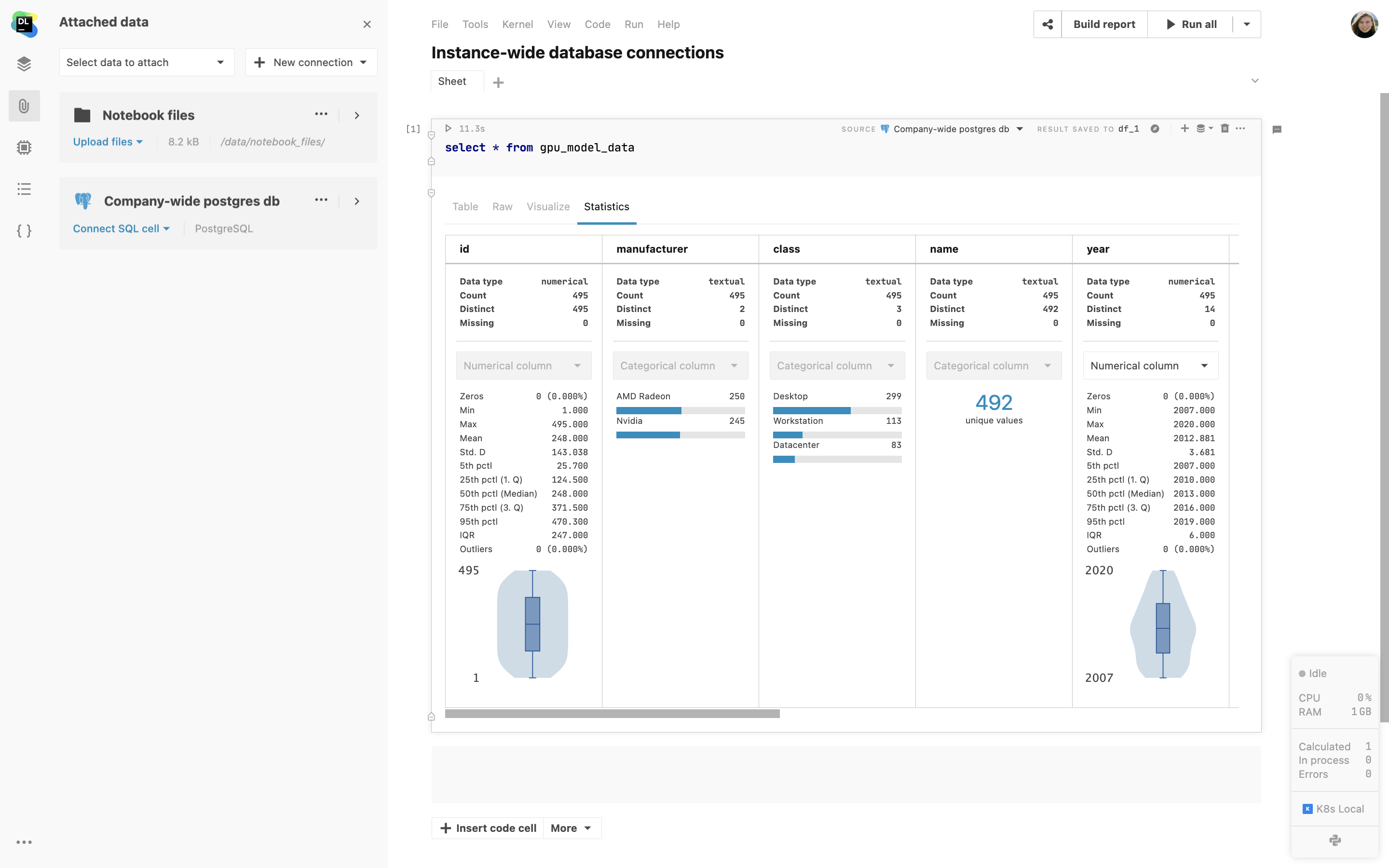
Instance-wide database connections
Help your team get straight to work and streamline new user onboarding with instance-wide database connections. Configure company-wide connections from the Data tab in the Admin panel. Datalore users will instantly see the new connection in shared and home workspaces.