Memory Profiling with Valgrind
Basics
Valgrind Memcheck is an instrument that allows you to find and identify memory errors in your C or C++ project. Valgrind Memcheck helps detect various problems such as memory leaks, invalid memory access, incorrect freeing of memory, or using of undefined values.
Valgrind Memcheck in CLion works on multiple platforms: Linux, macOS, and Windows via WSL.
Getting started with Valgrind Memcheck
To start using Valgrind Memcheck, you must pass several steps:
-
Install Valgrind Memcheck on your system. Following successful installation, CLion automatically detects Valgrind Memcheck by searching for it in the standard locations defined by the system
PATHvariable.For WSL, you need to install Valgrind on your WSL instance (
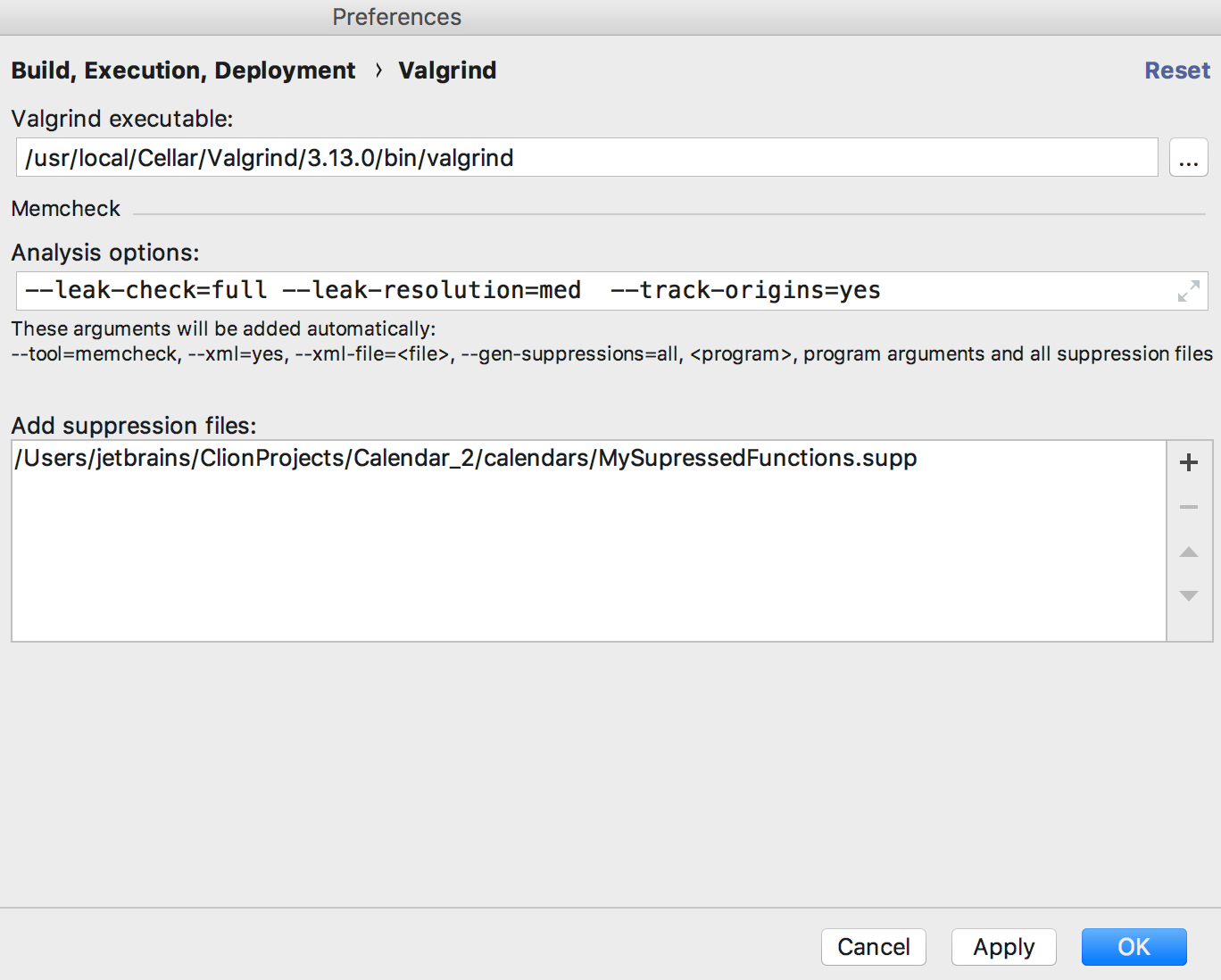
sudo apt-get install valgrind) and provide CLion with a path to the executable (see the next step). - In case of non-standard location of Valgrind Memcheck executable, you can point CLion to it explicitly: go to the (or if you are on macOS) menu option and specify it in the Valgrind Memcheck executable field of the dialog.
- In this dialog, specify the required analysis options.
- Configure a list of suppression files which can be used. For example, you may want to add a non-default suppression file to turn off Valgrind Memcheck checks on some particular libraries you are using in your project. The typical case here, for example, would normally be to suppress OpenSSL or Boost.
Now you have Valgrind Memcheck installed and configured and are able to run targets and tests with it.
Running targets
To run a target with Valgrind Memcheck, do one of the following (assuming that you have already selected the desired Run/Debug configuration):- On the main menu, choose option.
- In the Navigation bar, select the special icon, as follows:
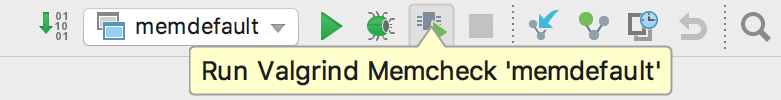
- Click
 gutter icon and select Run 'your_target_name with Valgrind Memcheck' option from the menu:
gutter icon and select Run 'your_target_name with Valgrind Memcheck' option from the menu: 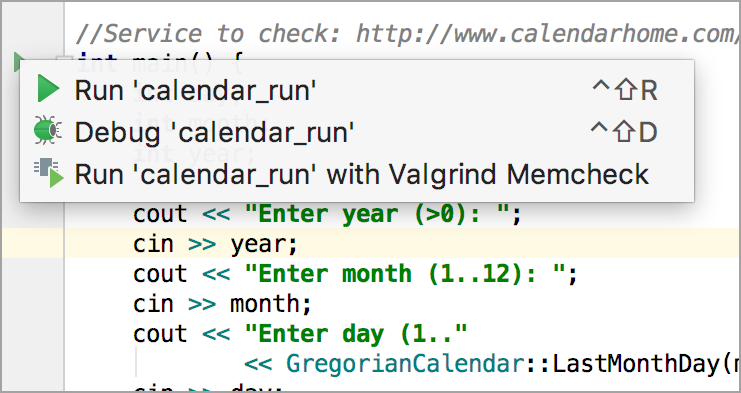
- Left pane of Valgrind tab of the Run tool window represents information of all the diagnostics, found by Valgrind Memcheck and related stack-traces. Each stack-frame shows us instruction pointer, problematic function name and source file (if possible) where problem is located.
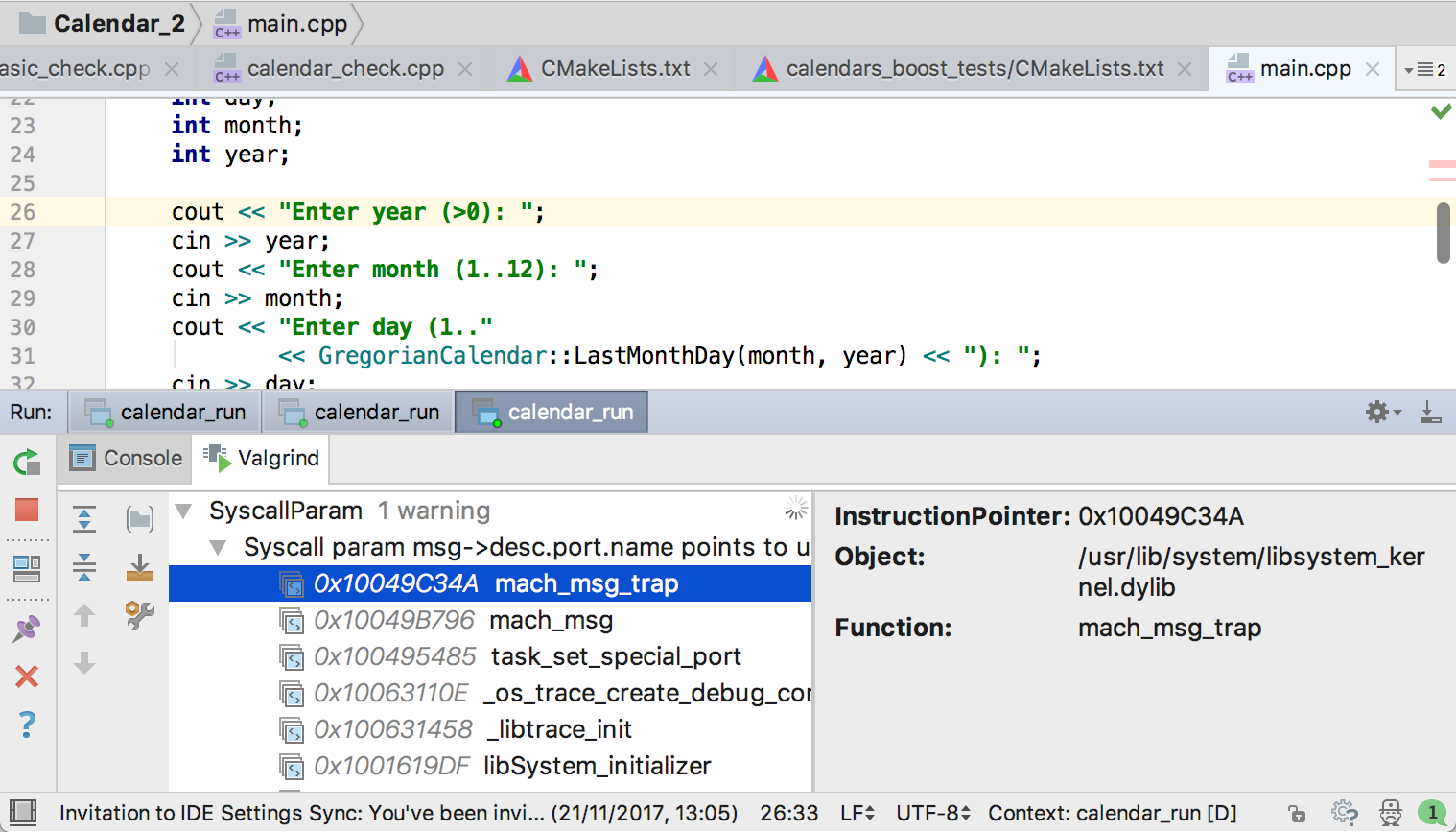
- Select a stack-trace of interest. On the right pane you can observe the full stack frame description of a target stack-trace and corresponding code preview (when possible). Press F4 to jump to corresponding source code and edit it as necessary.
- Right click the selected item to exclude it from the current results log or suppress the function that causes an error by adding a corresponding record to the selected suppression file.
Running tests
In the same way you can run your tests with Valgrind Memcheck:
- Select the desired test target.
- Click the icon of Navigation bar or Gutter and run the test.
- Explore results in Run tool window.