Docker Registry settings
Specify the settings for accessing the Docker registry used to store and distribute Docker images.
Enable the Docker plugin
This functionality relies on the Docker plugin, which is bundled and enabled in CLion by default. If the relevant features are not available, make sure that you did not disable the plugin.
Press Ctrl+Alt+S to open settings and then select .
Open the Installed tab, find the Docker plugin, and select the checkbox next to the plugin name.
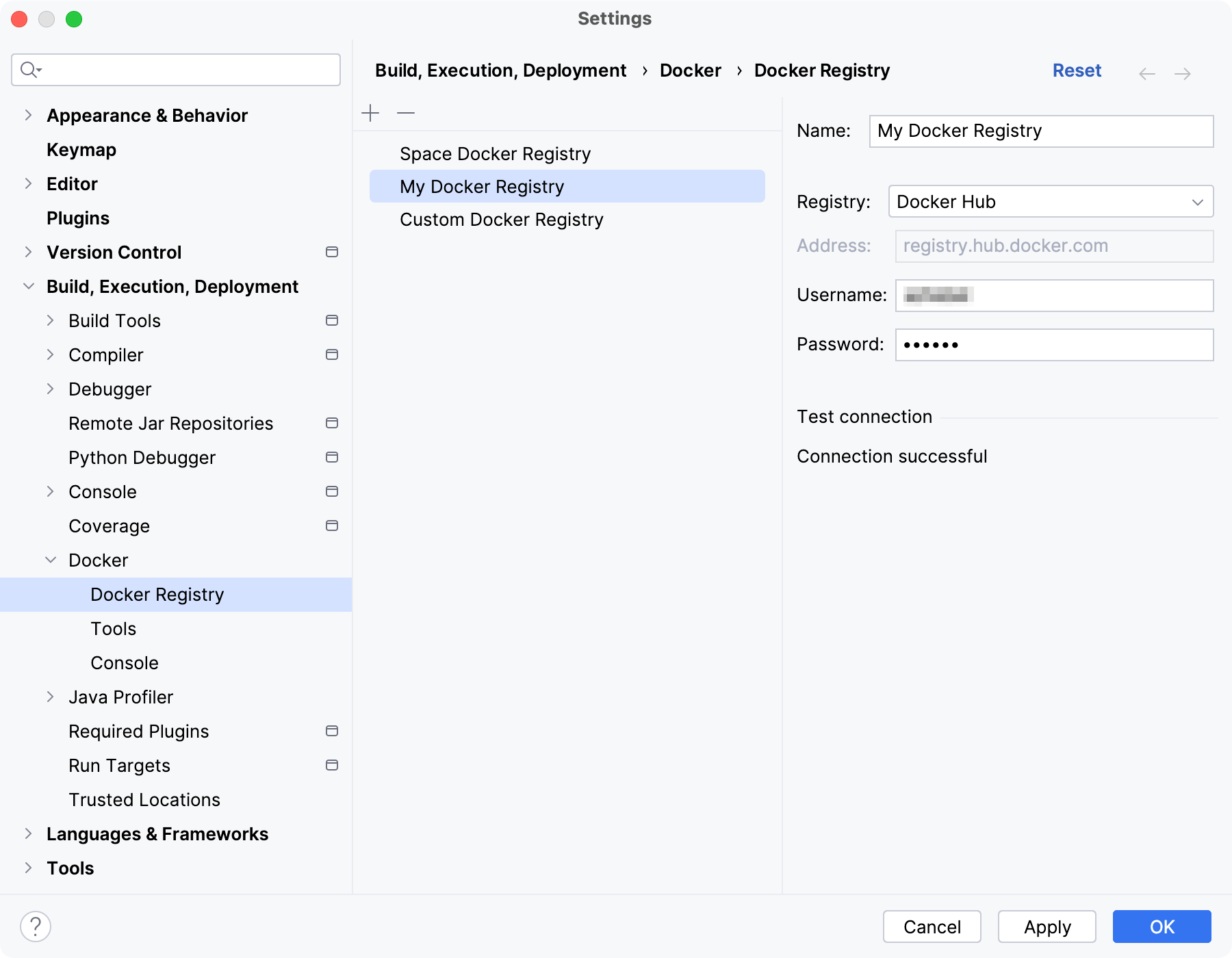
By default, CLion allows you to pull public images from Docker Hub. If you want to use a private repository, add a Docker registry and provide your account credentials.
Add
Add a new Docker registry.
Delete Alt+Delete
Remove the selected Docker registry.
For each Docker registry, configure the following:
- Name
Specify the name for this registry configuration.
- Registry
Select one of the available Docker registry types:
Docker Hub: specify your credentials to access private images in the main Docker registry at registry.hub.docker.com. By default, CLion can access only public images on Docker Hub.
GitLab: use the main GitLab registry at gitlab.com or specify a self-hosted GitLab registry.
JetBrains Space: use the Docker registry in your instance of Space.
Docker V2: specify any registry that supports Docker Registry HTTP API V2.
Generic: If other registry types don't work, add your registry as generic. You will not be able to browse and pull images in the Services tool window, but it will be possible to push images to this registry.
For example, CLion does not fully support the Quay image registry, but you can add it as a generic registry: create a repository on quay.io and specify
quay.ioas the address, your username and password.
- Address
Specify the URL of the Docker registry.
- Username
Specify the name of your user account in the selected registry.
- Password
Specify the password for your user account in the selected registry.
- Token
Specify the access token for the selected Docker registry
Azure Container Registry
CLion supports adding an Azure Container Registry as a Docker V2 registry.
If you are using a temporary token for individual login with Azure AD, set the username to 00000000-0000-0000-0000-000000000000 and the password to the token returned by az acr login with the --expose-token parameter. Use these commands to log in to the Azure CLI and expose the token:
If you want to use an admin user account, enable it in the Azure portal or via the Azure CLI:
You can set the admin username and password when configuring your Azure Container Registry.