Hub Permissions
A permission is an authorization granted to a user to perform particular operations. Permissions are granted to a user within a role, but not directly.
A role is a set of permissions that defines the level of access for a user to particular functionality and operations.
Permissions in Hub are divided in two categories:
Global permissions are granted at the global scope and do not depend on a specific project. For example, you cannot grant permission to create user accounts in a single project, you can do it only in the system-wide scope. Global permissions are marked with a
globalbadge in the list of permissions.Per-project permissions allow actions related to a specific project. For example, a role with the Read Project Basic permission grants users and groups access to view project properties and content for a specific project. If these users don't have the Read Project Basic permission for other projects in Hub, they don't have access to them.
Implied and Dependent Permissions
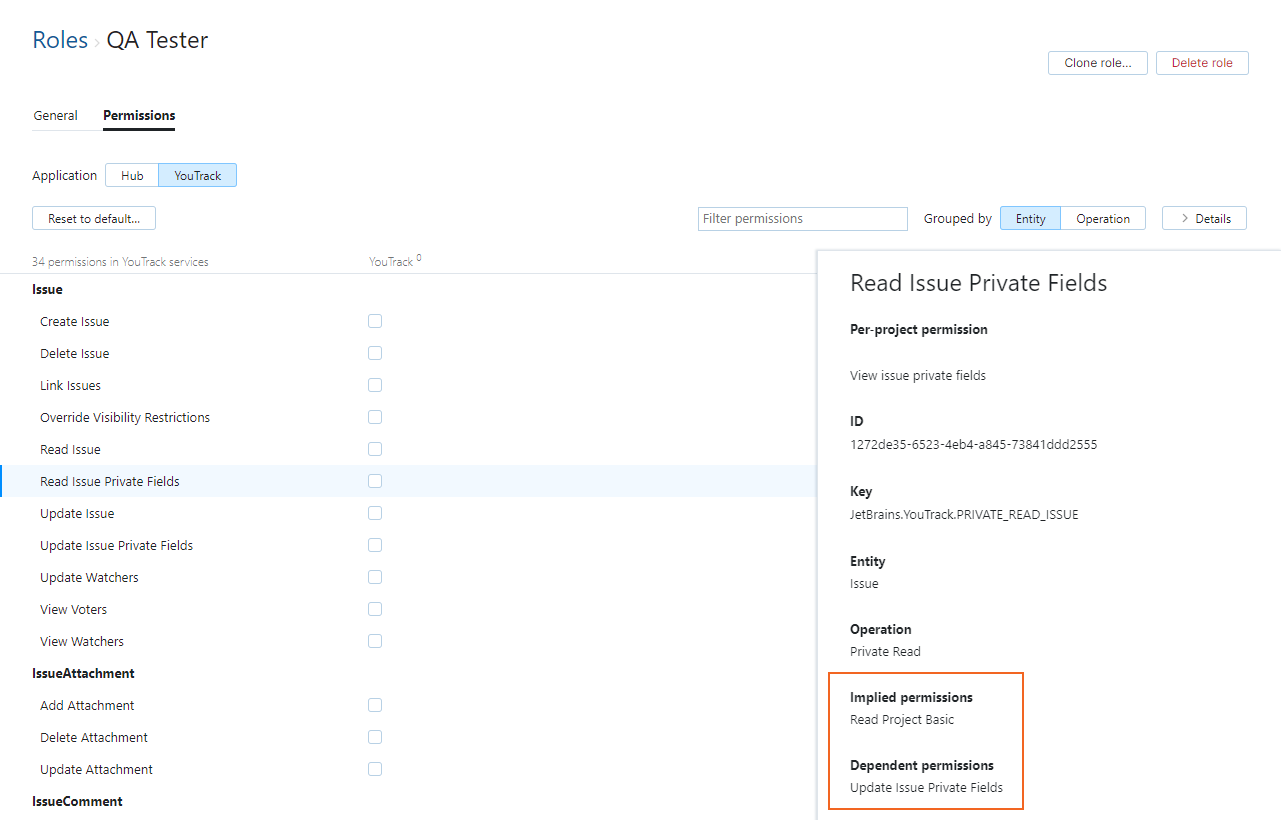
Implicit links connect permissions where actions that are granted by one permission are technically impossible without the other. This approach makes it easier to define custom roles with the appropriate access rights.
When you add a permission with implied permissions to a role, the implied permissions are added to the role automatically.
When you remove a permission with dependent permissions to a role, the dependent permissions are removed from the role automatically.
For example, the Read Project Basic permission (from the Hub service) is automatically added to a role when you add either Read Issue or Create Issue permission from the YouTrack service. It's technically impossible to view or create issues without being able to read basic project properties like the project name and project ID, so the Read Project Basic permission is granted implicitly.
To view the sets of implied and dependent permissions, select a permission and open the Details panel in the sidebar.
Generic Permissions
The following permissions are not related to specific entities in the system. These permissions are available at the global level.
Permission | Description |
|---|---|
Low-level Admin Write | Manage low-level administrative actions. Includes permission to integrate with third-party services and back up the database. Implies Low-level Admin Read. |
Low-level Admin Read | Read-only access to low-level administrative settings. Includes permission to view integrations with third-party services and metrics. |
Group-related Permissions
The following permissions grant access to group-related actions. These permissions are all available at the global level.
If you want to grant users fine-grained access to read and update specific groups, you can set values for the Visible to and Updatable by settings at the group level. For more information, see Edit Basic Group Settings.
Permission | Description |
|---|---|
Create Group | Create new groups. |
Delete Group | Delete groups. Implies Read Group. |
Read Group | View the list of groups, read group properties, and view subgroups. When combined with other permissions, the following access rights are granted:
|
Update Group | Edit group properties and manage subgroups. When combined with other permissions, the following access rights are granted:
Implies Read Group. |
Organization-related Permissions
The following permissions grant access to organization-related actions. These permissions are all available at the global level.
Permission | Description |
|---|---|
Create Organization | Add new organizations to the system. Implies Read Organization. |
Delete Organization | Permanently remove organization records from the system. Implies Read Organization. |
Read Organization | View organizations and their attributes. |
Update Organization | Edit organization attributes, manage project assignments and access rights. Implies Read Organization. |
Project-related Permissions
The following permissions grant access to project-related actions.
The Create Project permission is granted at the global level.
All other project-related permissions are granted on a per-project basis.
Permission | Description |
|---|---|
Create Project | Create new projects. |
Delete Project | Delete projects. Implies Read Project Full. |
Read Project Basic | View basic project properties. Basic project properties include the name, description, logo, and project owner. When combined with other permissions, the following access rights are granted:
|
Read Project Full | View all project properties. Users who are granted this permission can view the complete set of project settings. When combined with other permissions, the following access rights are granted:
Implies Read Project Basic. |
Update Project | Edit project properties and content, manage resources. Implies Read Project Full. |
Role-related Permissions
The following permissions grant access to role-related actions. These permissions are all available at the global level.
Permission | Description |
|---|---|
Manage Role | Modify the permission scheme using any of the following operations:
Implies Read Role |
Read Role | View the list of roles and the set of permissions that are assigned to each role. When combined with other permissions, the following access rights are granted:
|
User-related Permissions
The following permissions grant access to user-related actions. These permissions are all available at the global level.
Permission | Description |
|---|---|
Create User | Create new user accounts. Invite users to register their own accounts. |
Delete User | Delete user accounts. Implies Read User Full. |
Read User Basic | View the list of registered users and read the ID, username, name, and avatar for each user. Does not grant permission to view values for custom attributes. With Update Group, users can manage group memberships. |
Read User Full | View all properties for all registered users, including custom attributes and authorization details. Implies Read User Basic. |
Update Self | Edit all profile attributes for their own accounts. |
Update User | Edit all user profile data. Ban, merge, and anonymize user accounts. Implies Update Self and Read User Full. |