OpenID 2.0 Auth Module
When a user created manually in Hub logs on with OpenID for the first time, Hub ties the OpenID user to the existing Hub user if a matching email address or username is found. If no match is found, a new account for the OpenID user is created in Hub.
Enable OpenID Authentication
To allow users to sign in to Hub with OpenID authentication, enable an OpenID authentication module.
To enable OpenID authentication module:
From the main navigation menu, select Auth Modules.
Select the existing OpenID 2.0 authentication module from the list.
Configure the optional settings for the authentication module. For more information, see Additional Settings.
Click the Save button to apply the settings.
Click the Enable button.
The OpenID 2.0 authentication module is enabled.
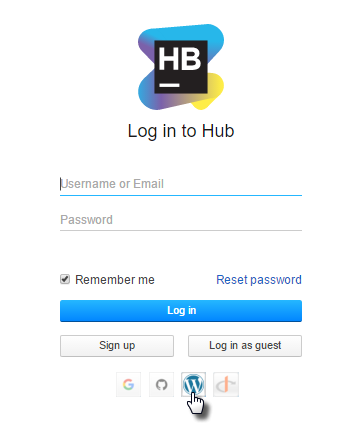
The icon stored in the Button image setting is added to the login dialog window. Users can click this icon to log in to Hub with their OpenID credentials.
Settings
The settings are configured automatically when the module is added to Hub. You do not have to change these settings. To configure the options that define how Hub treats new user accounts with OpenID credentials, see Additional Settings.
Field | Description |
|---|---|
Type | Displays the name of the application or service that is enabled for third-party authentication in Hub. |
Name | Stores the name of the authentication module. Use this setting to distinguish this module from other authentication modules in the Auth Modules list. The name is also shown in the tooltip for the third-party service icon on the login form. |
Button image | Displays the image used for the button that a user clicks to log in to Hub with their account in the connected authorization service. You can upload a JPG, GIF, or PNG file. The image is resized to 48 x 48 pixels automatically. |
Server URL | Stores the URL of the OpenID provider used to authenticate a login request in Hub. |
Schema
Use the following settings to map user data stored with the OpenID provider to user accounts in Hub.
Field | Description |
|---|---|
Stores the location that contains the email address. | |
First name | Stores the location that contains the first name of the user. |
Last name | Stores the location that contains the last name of the user. |
Full name | Stores the location that contains the full name of the user. |
Avatar | Stores the location that contains the avatar of the user. |
Additional Settings
When a user logs in to Hub with an OpenID account for the first time, Hub checks if an account with the same email address exists. If an account with the same email address exists, the OpenID credentials are added to the existing account.
Use the following settings to configure how Hub manages user accounts. These settings also let you reduce the loss of processing resources consumed by idle connections.
Option | Description |
|---|---|
User creation | Enables creation of Hub accounts for unregistered users who log in with an account that is stored in the connected authorization service. Hub uses the email address to determine whether the user has an existing account. |
Email auto-verification | Determines how Hub sets the verification status of an email address when the authentication service does not return a value for this attribute. |
Auto-join groups | Adds users to a group when they log in with an account that is stored in the connected authorization service. You can select one or more groups. New users that auto-join a group inherit all the permissions assigned to this group. We recommend that you add users to at least one group. Otherwise, a new user is only granted the permissions that are currently assigned to the All Users group. |
Connection timeout | Sets the period of time to wait to establish a connection to the authorization service. The default setting is 5000 milliseconds (5 seconds). |
Read timeout | Sets the period of time to wait to read and retrieve user profile data from the authorization service. The default setting is 5000 milliseconds (5 seconds). |
Audit | Links to the Audit Events page in Hub. There, you can view a list of changes that were applied to this authentication module. |
Actions
The following actions are available in the header:
Action | Description |
|---|---|
Set default | Designates the authentication module as the default for your installation. Only one authentication module can be set as the default at any time. If another module is currently set as the default, that state is cleared. This option is only shown when the current authentication module is not designated as the default. |
Clear default | Removes the authentication module as the default for your installation. If none of the available authentication modules are designated as the default, unauthenticated users are always directed to the Hub login page. This option is only shown when the current authentication module is designated as the default. |
Disable module | Disables the authentication module. This option is only shown when the authentication module is currently enabled. |
Enable module | Enables the authentication module. This option is only shown when the authentication module is currently disabled. |
Delete module | Removes the authentication module from Hub. Use only when you have configured additional authentication modules that let users log into your Hub installation. |